Straight Talk: New Yorkers on Privacy
We spent last week in New York doing field work on mobile messaging. Thank you to the Design Insights Group at Blue Ridge Labs for connecting us to such great participants. Many thanks also to the research participants themselves, who gave us permission to share their stories and images.

Apartment building in Brownsville (left); jewelry store + phone center in Harlem (right).
Real New Yorkers with Real Stories
We talked with twelve New Yorkers from across the city, meeting with people in libraries, offices, restaurants, and homes. We spent an hour listening to each participant talk about how they currently message, their privacy concerns and security practices, and their opinions on secure messaging. These conversations provided insights into how to design secure communication tools for a mass audience.

Learning how real New Yorkers use mobile phones by interviewing them.
Most participants were Android users, with one iPhone user and one person declining to say. All of them used multiple messaging apps on the same phone, with the native messaging app, WhatsApp, Kik, and Facebook Messenger the most commonly used, along with direct messages in Twitter or Instagram. Many people have developed a hierarchy based on how well they know someone to determine how they message them: letting someone know your Instagram handle is less intimate than giving them your phone number.
Emoji for Fun and Security
Going out into the field is always surprising. One unexpected insight during this research was participants’ use of emoji as a privacy-preserving strategy. Emoji were an important part of messaging for many people, with apps like Bitmoji and Expresser used to add graphics across multiple platforms. One teenaged participant even used emoji in place of names in her contact list; the people with emoji were the most intimate or frequently messaged.
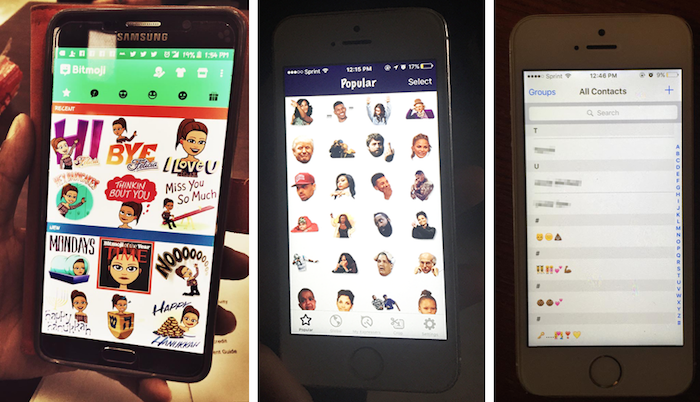
Left to right: Bitmoji, Expresser, and a participant’s contacts list.
Using emoji to hide the names of contacts can be an effective strategy if, like these participants, your main privacy concerns are related to other people getting physical access to your device. Shoulder surfing, people rifling through your phone, and screenshotting were some of participants’ top worries. Concealing the name through emoji makes it more difficult to identify the contact at a glance.
Stay tuned for more research findings and design directions from this work.