Behind-the-Scenes: Emerging Conversations from Slack
Thank you to everyone contributing to the Simply Secure Slack channel. If you’re interested in joining, email slack@simplysecure.org for an invitation. I’m especially eager to get more UX people in privacy and security involved, so spread the world. Here are some highlights from our recent Slack conversations.
Sharing the Rationale for UX Decisions
Check out Gabriel Tomescu’s The Anatomy of a Credit Card Form sharing the Wave design team’s process for arriving at an elegant, easy-to-use form. It includes a quote that spoke to me, “Given the existing mental model of paying with credit cards online, we felt the presence of one lock icon was sufficient.” Indeed.
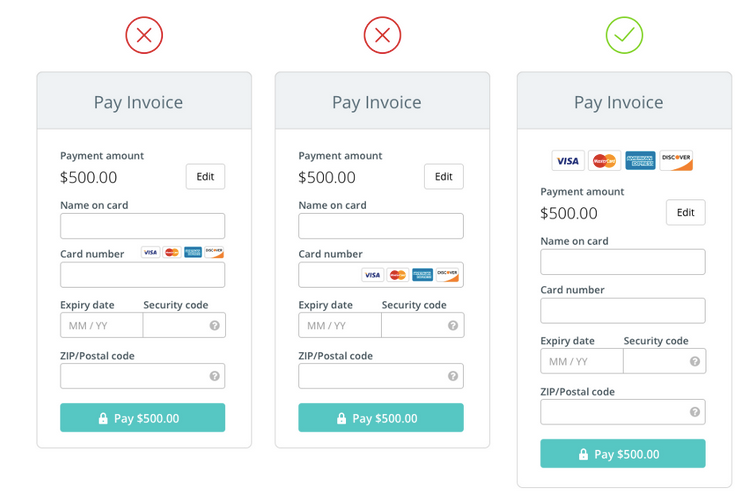
Subtle improvements to Wave’s credit card form
Communicating Technical Benefits vs. User Benefits
Stewart Butterfield wrote We Don’t Sell Saddles Here, which speaks eloquently to selling benefits of horseback-riding, not saddles. A technically savvy crypto audience will happily geek out about the details of different saddles. Meanwhile everyday computer users are still puzzling, “This helps me ride a horse? But why? And how does this help?”.
Security: Cuddly and Fierce
Tunnel Bear’s brand is more about horseback-riding than saddles. Their website doesn’t lead with “VPN” to describe what it is. Instead of shields, locks, or keys they use bears. Bears!


Tunnel Bears are approachably cuddly, but also fierce
Look for me at SOUPS in Ottawa this week. I’ll be presenting a lightning talk on ”Security is Not Enough: Design for Security Engagement” on Thursday afternoon. I’d love to chat if you’re there.